Product Introduction
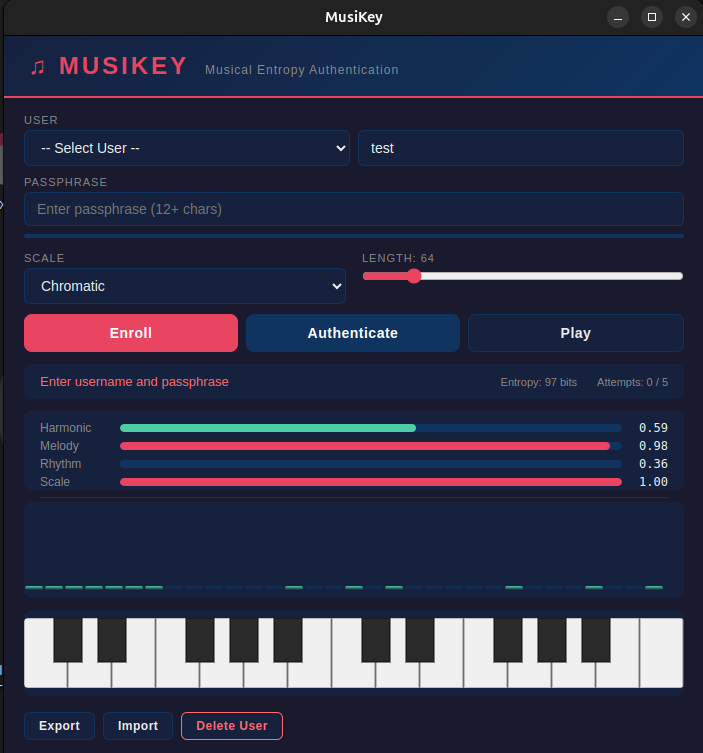
- Definition: Musikey is a novel authentication system (categorized under cybersecurity and identity access management) that replaces traditional alphanumeric passwords with a unique musical key sequence. Users authenticate by playing or selecting a specific sequence of notes or chords.
- Core Value Proposition: Musikey exists to provide a more memorable, engaging, and potentially more secure authentication experience compared to conventional passwords. It directly addresses password fatigue, weak password creation, and the vulnerability of passwords to phishing and brute-force attacks by leveraging auditory memory and musical patterns.
Main Features
- Musical Key Authentication:
- How it works: Users create an authentication key by selecting a sequence of musical notes, intervals, chords, or a short melody during setup. Authentication involves reproducing this exact sequence via an interface (e.g., virtual keyboard, MIDI input, or note selection grid).
- Technology: Likely employs audio fingerprinting or symbolic music representation (MIDI data) to capture and compare the input sequence against the stored key template. Secure cryptographic hashing would protect the stored representation.
- User-Centric Key Creation:
- How it works: The setup process guides users to create a personal musical sequence. This could involve selecting notes visually on a staff or keyboard, humming a tune converted to notes, or tapping a rhythm mapped to pitches. The system enforces minimum complexity rules (e.g., sequence length, required note variation).
- Technology: Utilizes intuitive UI/UX design principles for music input, potentially incorporating basic pitch detection algorithms or visual mapping tools.
- Adaptive Authentication Interface:
- How it works: Musikey offers different input methods (e.g., simple note selector for beginners, piano roll for musicians, MIDI input for professionals) to accommodate varying levels of musical knowledge and available hardware.
- Technology: Responsive web design frameworks ensure the authentication interface works seamlessly across devices (desktop, mobile, tablet). MIDI API integration enables direct input from musical instruments.
Problems Solved
- Pain Point: Password fatigue and weak password practices. Users struggle to remember complex, unique passwords for numerous accounts, leading to password reuse and easily guessable choices, significantly increasing security risks.
- Target Audience:
- General Users: Individuals overwhelmed by managing numerous complex passwords seeking a more intuitive and memorable login method.
- Musicians & Music Enthusiasts: Users with musical training or strong auditory memory who find recalling a musical sequence significantly easier than random strings.
- Security-Conscious Individuals: Users seeking alternatives to traditional passwords vulnerable to phishing, keyloggers, and brute-force attacks.
- Accessibility Advocates: Potential for aiding users with certain cognitive or memory challenges who respond better to auditory/pattern-based recall (dependent on specific implementation).
- Use Cases:
- Personal Account Logins: Securing email, social media, and streaming service accounts with a memorable musical key.
- Creative Platform Access: Authentication for music production software, online DAWs, or sheet music libraries where a musical key feels contextually appropriate.
- Secondary Authentication Factor: Serving as a more engaging and memorable second factor in a multi-factor authentication (MFA) setup.
Unique Advantages
- Differentiation: Unlike password managers (which store credentials) or biometrics (which rely on physical traits), Musikey offers a fundamentally different type of secret: a user-created musical sequence. It contrasts with traditional passwords by leveraging auditory memory and pattern recognition, potentially offering higher memorability and resistance to common text-based attacks.
- Key Innovation: The core innovation is the translation of authentication security into the domain of music cognition and pattern recall. It replaces abstract character strings with structured auditory sequences, potentially tapping into different, and for some, stronger, memory pathways. The security relies on the complexity and secrecy of the musical sequence itself.
Frequently Asked Questions (FAQ)
- Is Musikey more secure than a traditional password? Musikey's security depends on the complexity and secrecy of the musical key. A sufficiently long and complex sequence (e.g., 8+ distinct notes/chords with varied intervals) can be highly resistant to brute-force guessing, potentially offering comparable or superior security to strong passwords, especially against automated text-based attacks. However, its vulnerability to acoustic eavesdropping or sophisticated replay attacks needs evaluation.
- Can I use Musikey if I'm not musical? Yes, Musikey is designed for users of all musical backgrounds. The interface typically provides simple visual selectors (like clicking notes on a keyboard or grid) rather than requiring instrumental skill. Creating and remembering a short, distinct sequence of notes is achievable without formal training.
- How does Musikey prevent someone from overhearing my musical key? While a potential risk, overhearing a sequence of notes is generally harder to accurately reproduce immediately than seeing a password typed (shoulder surfing). The system may also incorporate mechanisms like randomized note layouts per session or require tempo/rhythm elements to mitigate simple replay. For high security, combining it with another factor is recommended.
- What happens if I forget my Musikey sequence? Like any authentication system, Musikey requires a secure account recovery process. This typically involves fallback methods such as email verification, security questions, or backup codes established during initial setup to regain access if the musical key is forgotten.
- Can Musikey be integrated with other apps or websites? As an authentication standard, Musikey would require adoption by service providers (websites, apps) who integrate its API. Its feasibility as a standalone app or browser extension managing logins across sites would depend on its specific technical implementation and security protocols (e.g., password manager-like functionality using musical keys).